
Leading in times of crisis: How healthy optimism works
Crises are as much a part of business as stormy weather at sea. But what if the storm lasts longer? 3 impulses for strong leadership in a crisis.
It sounds like a play on words but it’s nothing less than a paradigm shift: Secure IT by Design means building software, hardware and networks securely from the very beginning instead of fixing vulnerabilities subsequently. Higher initial costs will pay off in the long run.
It’s an unpleasant truth: Somewhere in the world, every few days, a new data scandal comes to light. Recently it was revealed that hackers were able to view millions of airline customer data files, including credit card numbers. Another example is an armaments company, confronted with a data leak: internal documents circulated on the Internet. Austrian authorities made headlines because confidential data of citizens was accessible on unprotected servers. Since the GDPR came into force, companies based in the EU have reported around 160,000 data leaks – in 2019, there were even more incidents than in the previous year. Such data breaches not only undermine the trust of customers and the public, there is also a threat of high fines and claims for damages.
The more complex a company’s IT landscape is, the greater the concern about neglecting security-critical aspects. In our experience, it is common practice to add new infrastructure, hardware and programs to existing systems – dealing with security gaps afterwards. For example, due to anti-pandemic measures companies quickly switched to remote work and set up numerous remote access points. In many cases, the systems were encrypted and the general security level was increased later on. The risk of reacting too late or overlooking something was comparatively high.
From an expert’s point of view, Security by design is a better strategy to protect companies from attackers and data loss. Here is a selection of criteria applying to the main IT segments:
Software
Hardware
Network
As already mentioned, this is just a selection of criteria that are relevant for security by design. Some, but not all, require higher investments from companies. Even if secure design may be more expensive at first, it will pay off over the years. Which priority should a company set? This is a complex question, requiring analyses that usually lead to larger projects. Therefore, many companies postpone the issue. In practice, we have often experienced that decision-makers don’t react before problems arise. In view of growing risks, more companies should move to precautionary measures and start a top to bottom change of their IT security practice.
Learn more about our cyber security consulting services here.

Crises are as much a part of business as stormy weather at sea. But what if the storm lasts longer? 3 impulses for strong leadership in a crisis.
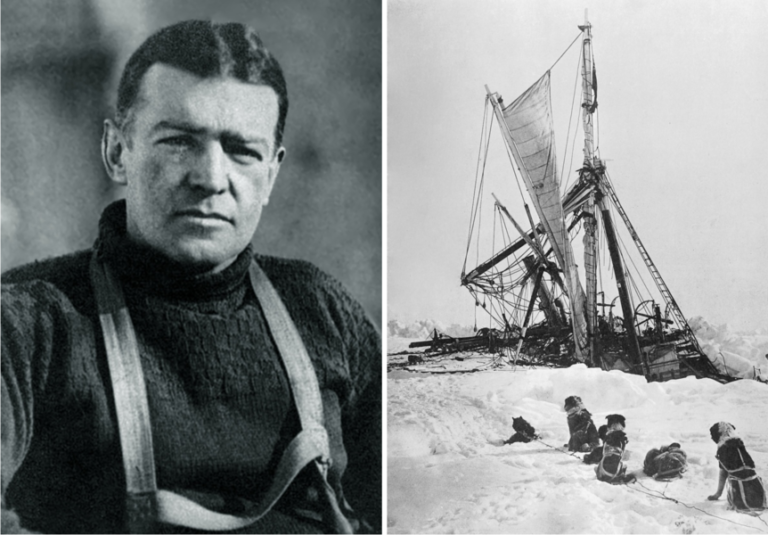
He conveyed confidence in a desperate situation: British polar explorer Ernest Shackleton and his team survived a two-year battle for survival in the Southern Ocean. What can leaders learn from him in times of crisis?
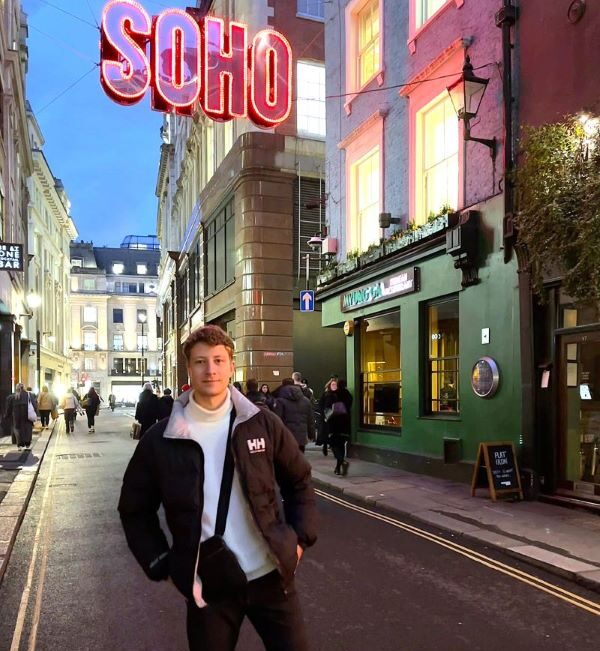
Getting an IT project across hundreds of organizational units to the finish line? Our colleague Mathis takes a sporty approach. In our interview, he tells us what excites him about project management as a consultant and why he goes to the boxing ring to compensate.
2021 Grosse-Hornke Private Consult